Did you know that standard search engines index less than 10% of the total internet? While Google and Bing focus on the surface web, tools like Ahmia crawl the hidden layers of the Tor network. As interest in digital anonymity grows, many users wonder if querying these indexes compromises their identity or exposes them to legal liability.
The concern is valid. Unregulated onion services host everything from legitimate privacy forums to outright malware. Understanding how Ahmia filters that landscape is the most effective way to assess your actual threat surface before you click a single result.
This guide breaks down how Ahmia handles user data, the mechanics behind its blacklist, and the inherent attack vectors of any dark web search index. We also compare Ahmia against other prominent Tor engines so you can decide which tool matches your experience level. For a complete walkthrough of setup and access, see our pillar guide to using Ahmia safely in 2026.
Quick Answer — Is Ahmia Safe?
Ahmia is widely regarded as the most reputable search index for Tor hidden services, owing to its open-source architecture and actively enforced blacklist. The primary threat does not come from the search engine itself but from the unregulated external sites it surfaces in results. Users who stick to verified entry points and maintain strict browser configurations face minimal risk from the platform directly.
What Is the Ahmia Search Engine?
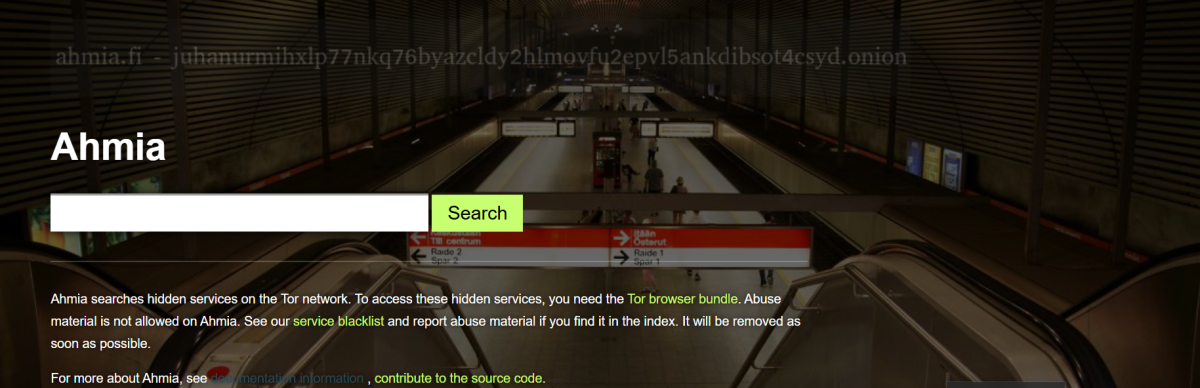
Ahmia is a specialized search engine that crawls and indexes ".onion" sites operating within the Tor network. The project is developed as a non-profit initiative — documented on its public GitHub repository — to provide a search alternative that deliberately ignores personal identifiers. Unlike commercial engines that monetize behavioral data, Ahmia's architecture is designed to function without collecting it.
The system deploys web crawlers that navigate Tor hidden services and build a searchable database. Because the entire codebase is open-source, security researchers can audit the crawler logic, indexing behavior, and filtering mechanisms independently. This transparency is why the project is frequently cited in academic research on Tor topology and cited as a reliable starting point on directories like onionlinks.live. It functions as a bridge between standard web protocols and the Tor network — but that bridge only extends so far.
Why Threat Vectors Exist on Any Tor Search Engine
Ahmia's own infrastructure follows standard hardening practices. The danger lies in what it indexes:
- Unregulated Content: No central authority on Tor can enforce takedowns of scams, phishing pages, or malicious payloads.
- Exploitative Scripts: Some indexed sites host code designed to exploit browser vulnerabilities or de-anonymize visitors.
- User Error (Identity Linkage): The most common breach occurs when users accidentally associate their real-world identity — a personal email address, a reused username — with activity on an indexed forum.
- Mirror and Phishing Sites: Scammers routinely create convincing duplicates of legitimate search engines to intercept traffic and log queries.
Understanding the underlying architecture helps clarify why these risks persist. For a deeper explanation of how the network itself handles routing and anonymity, read our guide to what Tor is and how it works.
The Ahmia Blacklist Explained
One of Ahmia's defining features is its active moderation layer. The Ahmia blacklist is a continuously updated database of onion addresses that the search engine explicitly refuses to crawl, index, or display in results.
According to the project's published filtering policy on GitHub, this blacklist primarily targets sites hosting illegal imagery and exploitative material. By implementing this filter at the crawler level — before content ever reaches the index — Ahmia positions itself as an "ethical" search tool within the Tor ecosystem. This dramatically reduces the likelihood of accidental exposure to the most severe categories of content found on completely unmoderated directories.
Common OPSEC Failures When Using Tor Indexes
Curiosity about hidden services continues to climb — our analysis of darknet desires and trends in 2026 shows that interest outpaces operational security knowledge by a wide margin. Users typically compromise themselves through these specific errors:
Relying on Unverified URLs
Searching for Ahmia on clearnet engines often surfaces "proxy" sites or phishing mirrors that log queries and inject tracking.
Mitigation: Access should only occur through verified Tor-compatible entry points. Cross-reference addresses using our official Ahmia onion link verification guide or a vetted directory like onionlinks.live.
Leaving JavaScript Enabled
Scripts remain a primary vector for identifying real IP addresses or harvesting device fingerprints.
Mitigation: The Tor Project documentation recommends setting the browser security slider to "Safest" to universally disable JavaScript before accessing any hidden service.
Mobile App Risks
Users sometimes search for an "Ahmia APK" to bypass mobile browser limitations.
Mitigation: No official app exists. Downloading third-party APKs introduces severe privacy implications — potentially keyloggers, traffic interceptors, or trojanized builds. Mobile users should rely solely on the official Tor Browser. We document the full scope of these mobile-specific threats in our Ahmia APK 2026 safety analysis.
Downloading Unverified Files
Executable files or documents from onion sites frequently contain trojans or ransomware payloads.
Mitigation: Treat all downloads from Tor search results as potentially compromised. Open documents in isolated environments, and avoid executing binaries entirely unless you can verify the source.
Ahmia vs. Other Dark Web Search Engines
To contextualize Ahmia's risk profile, it helps to compare it against other prominent tools. If you are evaluating the top dark web search engines of 2026, the differences in moderation and indexing policy are the most critical differentiators.
| Feature | Ahmia | Torch | Not Evil | Hidden Wiki |
|---|---|---|---|---|
| Moderation | High (Active Blacklist) | Low (Unmoderated) | Medium (Basic filters) | None (Static link list) |
| Primary Risk | External indexed sites | Aggressive ads, dead links | Unfiltered explicit results | Phishing, illegal content |
| Threat Surface | Low (Best for beginners) | High | Medium | Very High |
| Index Size | Medium | Large | Medium | Small/Static |
Ahmia vs. Torch Search
Torch is one of the oldest indexes and maintains a massive database. However, it lacks the strict blacklist enforcement that defines Ahmia. Torch results frequently surface dead links and potentially harmful content with no warning, making it a poor choice for users prioritizing a reduced attack surface.
Ahmia vs. Not Evil
Not Evil aims for a relatively clean interface and applies some content filtering. However, Ahmia maintains a more transparent and rigorously enforced blacklist against abusive material, with the filtering logic itself open to public audit.
Ahmia vs. The Hidden Wiki
The Hidden Wiki is not a search engine but a static directory of links. It is notoriously unmoderated, serves as a primary vector for phishing scams, and makes no effort to filter illegal content. Ahmia presents a significantly lower risk profile than any iteration of the Hidden Wiki.
Decision Framework: Which Tool Matches Your Experience Level?
| Experience Level | Recommended Tool | Why |
|---|---|---|
| Beginner | Ahmia only | Active blacklist, open-source code, minimal exposure to severe content |
| Intermediate | Ahmia + Not Evil | Broader index access with moderate filtering on both |
| Advanced | Any (with strict OPSEC) | Experienced users can navigate unmoderated indexes, but should still default to Ahmia for general queries |
Safe Browsing Checklist
Before accessing any Tor search engine, confirm the following:
- Tor Browser security slider set to "Safest"
- JavaScript disabled universally
- URL verified through a trusted directory or our official Ahmia URL guide
- No personal identifiers (email, username, real name) entered into any onion site
- No files downloaded or executed from search results
- No third-party APKs installed — official Tor Browser only on mobile
- Bridge configured if hiding Tor usage from your ISP is required
Frequently Asked Questions
Is it illegal to query the Ahmia search engine? No. Using a search engine, including Ahmia, is legal in most jurisdictions. It is an information retrieval tool. Legality depends entirely on subsequent actions — such as purchasing illicit goods or accessing prohibited content — not the act of searching.
Does Ahmia log my IP address or search queries? Because Ahmia is accessed via the Tor network, the server only registers the IP address of the Tor exit node, not the user's actual IP address. The project states it does not store personally identifiable search data, and the open-source codebase allows independent verification of this claim.
Can my ISP see that I am using Ahmia? Your Internet Service Provider can see that you are connecting to the Tor network, but cannot see that you are specifically visiting Ahmia or what you are searching for. If concealing Tor usage from your ISP is necessary, the Tor Project recommends configuring a Bridge before connecting.
How do I ensure I am not on a fake Ahmia mirror? Avoid typing the URL manually. Cross-reference the official address through trusted privacy directories or use a bookmark created during a previously verified session. Our Ahmia official URL guide maintains current verified addresses.
Does Ahmia completely remove all dangerous content? No blacklist is perfect. Ahmia aggressively filters known illegal material, but it cannot guarantee that every indexed site is free of malware, phishing scripts, or scams. User vigilance and strict browser settings remain essential.
Conclusion
Exploring Tor search indexes does not have to mean accepting unnecessary risk — provided the tools are used with discipline. Ahmia stands out in the hidden services landscape because its open-source code and strict blacklist policies are designed to minimize exposure before a user ever clicks a result.
That said, the search engine's moderation does not extend to the sites it indexes. The boundary between a safe query and a compromised session is defined entirely by your own operational security. By maintaining strict browser configurations, relying on verified access points rather than third-party proxies, and treating every external link as potentially hostile, users can navigate these resources while keeping their threat surface minimal.
For ongoing updates on verified addresses and configuration changes, bookmark our complete Ahmia safety and access guide.