Meta Title: Deep Web vs Dark Web: Key Differences Explained 2026 Meta Description:
Disclaimer: This guide is for educational and cybersecurity awareness purposes only. It does not promote, encourage, or provide instructions for illegal activity.
Deep Web vs Dark Web: Key Differences Explained 2026
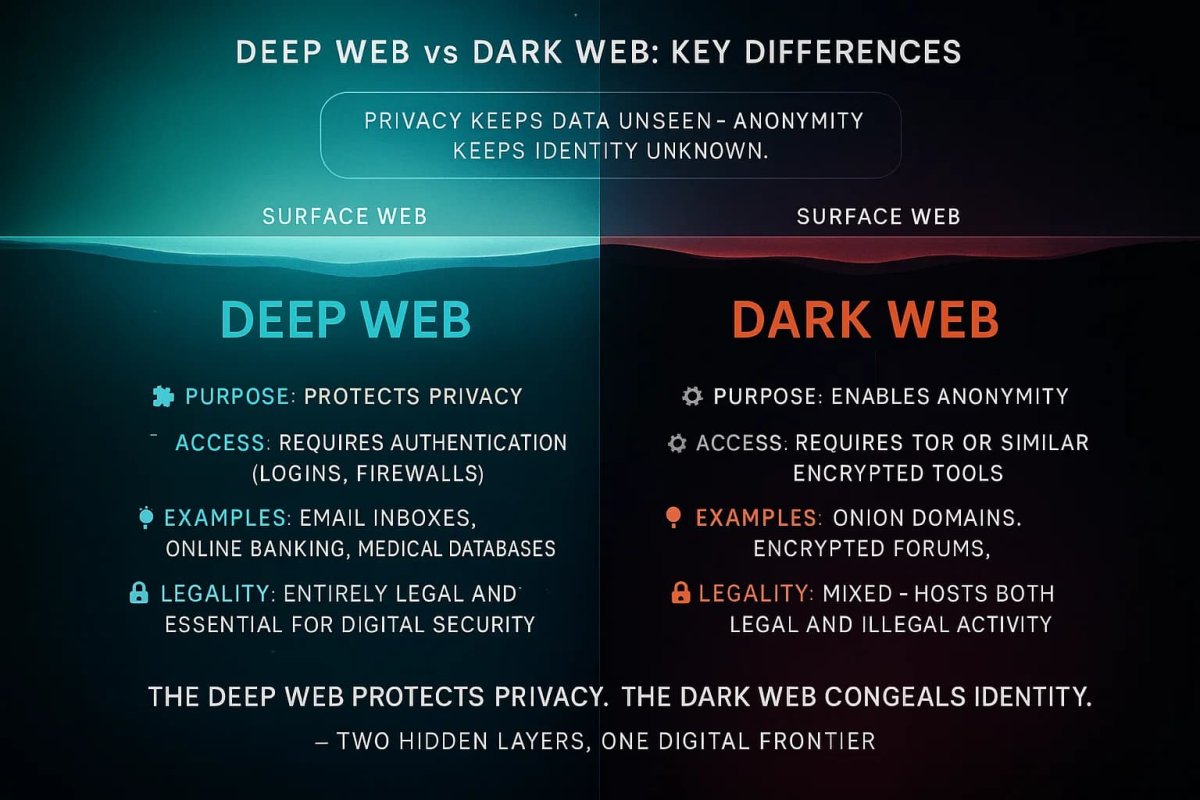
📌 Deep Web vs Dark Web vs Dark Net (In One Sentence):
- Deep Web = Private, unindexed content
- Dark Web = Hidden services requiring special access
- Dark Net = Infrastructure enabling anonymity
99% of the internet is invisible—and most people don’t even know the difference between the Deep Web and Dark Web.
According to organizations like the Tor Project and cybersecurity firms such as Kaspersky and Norton, anonymity tools are designed for privacy—but user behavior remains the biggest risk factor. Understanding these layers is the first step toward mastering your digital footprint in an era where data breaches are the norm.
🌊 Why This Matters More Than You Think in 2026
You’re only seeing less than 5% of the internet.
Everything else exists below the surface—hidden from search engines, protected by logins, or intentionally obscured. You interact with the Deep Web every time you check your email, open a cloud storage drive, or log into your banking apps. If Google cannot crawl a page, it belongs to the Deep Web.
However, misunderstanding the terminology leads to severe consequences:
❌ False confidence in anonymity ❌ Poor privacy decisions ❌ Higher exposure to scams, tracking, and data leaks
In 2026, massive data breaches continue to flood dark web marketplaces with personal information. Meanwhile, AI-driven censorship drives more legitimate users to anonymizing tools.
👉 Knowing the difference isn’t optional anymore—it’s survival-level digital awareness.
🧊 The Internet Iceberg (Reality Check)
To clear up the confusion immediately, here is how these three distinct layers actually compare:
| Layer | What It Is | Size | How You Access It |
|---|---|---|---|
| Surface Web | Public sites (Wikipedia, YouTube) | <5% | Chrome, Safari |
| Deep Web | Private data (Email, Banking) | 90–95% | Login required |
| Dark Web | Hidden networks | <0.01% | Specialized tools |
🌐 Surface Web vs Deep Web (What Most People Get Wrong)
Think of the internet as an iceberg. The Surface Web is the visible tip. Sites like Wikipedia and Amazon allow search engine bots to crawl their pages. It's convenient, but it's also where your data is most frequently tracked.
Below that tip lies the vast Deep Web. Estimates from cybersecurity researchers suggest the Deep Web may be 400 to 500 times larger than the Surface Web.
| Feature | Surface Web | Deep Web |
|---|---|---|
| Visibility | Public | Hidden |
| Indexed | Yes | No |
| Security | Low–Medium | High (by design) |
| Purpose | Browsing, shopping | Private accounts, data |
The Deep Web exists to protect your privacy. This includes your private Google Drive files, medical records, university library databases, and internal company intranets.
👉 Key insight: The Deep Web isn’t dangerous—it’s what protects your data every day.
🕶️ The Dark Web: Privacy Tool or Risk Zone?
The Dark Web is a small, hidden portion of the Deep Web that requires specific software like the Tor Browser.
While the media portrays this area strictly as a hub for illegal activity, it is actually a neutral tool vital for journalists, whistleblowers, and people living under strict government censorship.
Technical Access Comparison: Deep Web vs Dark Web
To understand why the two require entirely different approaches, look at how they are built:
| Technical Aspect | Deep Web Access | Dark Web Access |
|---|---|---|
| Required Browser | Standard (Chrome, Safari) | Specialized (Tor Browser, I2P) |
| URL Structure | Standard (.com, .org) | Cryptographic (.onion, .i2p) |
| Network Connection | Standard ISP | Overlay network (Dark Net) |
| Encryption Level | Standard (HTTPS) | Multi-layered (Onion Routing) |
| Identity | Real login/credentials | Total pseudonymity |
How do you access the dark web safely? Finding links is the biggest challenge. Because there is no Google for the dark web, users must rely on unverified link directories routinely manipulated by scammers. To avoid phishing clones, security researchers often rely on carefully curated directories, such as a verified Onion Links directory, to map the network without falling into traps.
👉 Reality check: It’s not evil—but it’s not safe either.
🧠 Dark Net vs Dark Web: The Confusion Explained
Most people use these terms interchangeably, but they refer to two entirely different things:
- Dark Web = Content (the websites, forums, and services you view)
- Dark Net = Infrastructure (the network operating behind the scenes)
You must recognize the three primary Dark Net entities:
- Tor Browser: The most popular overlay network, relying on volunteer servers.
- I2P: A fully peer-to-peer network used for internal site hosting.
- Freenet: A highly decentralized network focused on censorship-resistant file sharing.
👉 Simple analogy: Dark Net = Roads | Dark Web = Destinations
🧅 How Onion Routing Works (Simplified)
The technology wraps your data in layers of encryption, much like the layers of an onion.
| Step | What Happens Behind the Scenes |
|---|---|
| 1. Connection | You connect using a specialized browser. |
| 2. Encryption | Data is wrapped in multiple encryption layers. |
| 3. Routing | Traffic passes through random global nodes. |
| 4. Exit | The final node (exit node) sends the request to the destination. |
| 5. Return | Data travels back through the exact same encrypted path. |
👉 Result: Strong anonymity—but significantly slower speed.
⚖️ Deep Web vs Dark Web: The Ultimate Side-by-Side Comparison
Despite the overlap (the dark web is technically part of the deep web), they serve very different purposes.
| Aspect | Deep Web | Dark Web |
|---|---|---|
| Size | ~90% of web content | < 0.01% of web content |
| Accessibility | Standard browsers + login | Special software (Tor) |
| Content | Private & Everyday | Anonymous & Often Illicit |
| Anonymity | Standard (Sites know who you are) | High (Users and owners hide identity) |
| Legality | 100% legal to access | Using Tor is legal; crime on it is not |
| Examples | Webmail, banking, intranets | Darknet markets, SecureDrop |
💼 Common Uses: The Good, The Bad, The Ugly
Not everything on the dark web is illegal, but it is famously a wild west of content. Keeping tabs on active dark web markets allows cybersecurity defenders to see what stolen data is being commodified.
| Use Case Category | ✔️ Legitimate Examples | ⚠️ Illicit Examples |
|---|---|---|
| Communication | ProtonMail .onion, SecureDrop | Encrypted chat for organized crime |
| Marketplaces | Privacy-focused digital stores | Drug sales, stolen credit cards, fake IDs |
| Media & Info | BBC News .onion, NYT .onion | Illegal pornography, extremist propaganda |
| Cybersecurity | Threat intelligence gathering | Ransomware-as-a-Service, hacker-for-hire |
👉 Brutal truth: The deep web holds the data; the dark web monetizes the stolen data.
⚠️ Dark Web Risks in 2026 (What Can Go Wrong)
The threat landscape has evolved drastically due to AI and advanced exploit techniques.
| Risk Type | What Actually Happens |
|---|---|
| AI-Generated Phishing | Scammers use AI to create perfect clones of legitimate hidden services in seconds. |
| Malware & Scams | Fake directories and clone sites steal credentials. Drive-by downloads target browsers. |
| VPN Misuse | Incorrect configuration can break your anonymity entirely. |
| Zero Customer Protection | If you send crypto to a scammer (an exit scam), you have zero recourse. |
Can you be tracked on Tor?
True anonymity is tricky. Tor hides your identity, but mistakes can expose you.
| Safe Behavior on Tor | Risky Behavior (How People Get Caught) |
|---|---|
| Disabling JavaScript | Logging into personal surface web accounts |
| Using the "Safest" security setting | Downloading files outside the Tor browser |
| Keeping window default size | Reusing a username from the clearnet |
Governments have zero-day exploits to identify users. The Federal Bureau of Investigation (FBI) has run numerous sting operations to unmask visitors’ IPs.
👉 Most exposures happen due to human mistakes—not technology failure.
🎭 Common Myths (Debunked Fast)
| 🚫 The Hollywood Myth | ✅ The Cybersecurity Reality |
|---|---|
| “Everything is illegal” | Many legitimate uses exist (journalists, activists). |
| “Tor = full anonymity” | One mistake (like reusing a username) can expose you instantly. |
| “90% of the web is dark web” | Wrong. 90% is the benign Deep Web. |
| “Hackers track your IP in seconds” | IP tracing is difficult; the real danger is user error. |
🚀 Why This Matters for Cybersecurity in 2026
As we move through 2026, the lines between layers are blurring. Major platforms are launching .onion versions to fight censorship. However, threats are evolving faster:
- AI-Generated Phishing: Perfect clones of sites created in seconds.
- Faster Networks: Eliminating the "slowness" barrier to entry.
- Decentralization: Harder to shut down scams, but harder to shut down illegal markets.
According to research from the National Institute of Standards and Technology (NIST), monitoring for leaked credentials is a recommended cybersecurity practice. For individuals and organizations looking to understand these hidden networks from an educational perspective, exploring comprehensive resources like Onion Links can provide valuable context.
🚨 Hard Truth: You Don’t Need to Visit the Dark Web to Be at Risk
Here is a hard truth: you don't have to visit the dark web to be a victim of it.
To understand the threat, look at the Stolen Data Lifecycle—how your information transitions from the safe Deep Web to the dangerous Dark Web:
| Stage | Location | What is Happening |
|---|---|---|
| 1. Safe Storage | Deep Web | Your data sits safely in your bank or email portal. |
| 2. The Breach | Deep Web | Hackers exploit a vulnerability or use phishing to steal the database. |
| 3. The Dump | Dark Web | Hackers upload the stolen data to a dark web marketplace. |
| 4. Monetization | Dark Web | Criminals buy your data for $1-$40 (passwords, SSNs, credit cards). |
| 5. Weaponization | Surface/Deep Web | Criminals use your data to commit fraud or break into other accounts. |
If you have used the internet for the last 10 years, there is a high probability that an old password already exists in a dark web database.
👉 The real risk isn’t visiting—the risk is already being exposed.
🧠 Final Verdict (The Only Thing You Need to Remember)
👉 Deep Web = Private 👉 Dark Web = Hidden 👉 Dark Net = Infrastructure
⚠️ The Biggest Mistake It’s not curiosity. 👉 It’s false confidence.
Reading guides or understanding the basics does not make you anonymous. Security failures happen because of small human errors, not technical flaws.
🔐 Final Takeaway Privacy tools reduce risk—they do NOT eliminate it.
And in 2026: 👉 Anonymity isn’t something you install—it’s something you practice.
❓ FAQ (High-Retention Format)
Is it illegal to browse the Dark Web? No. Browsing is legal in most countries. Illegal actions are not. (Think of it like a car: driving is legal, speeding is not).
How much of the internet is the deep web? The deep web makes up the majority of the internet—at least 90% of all web pages. The dark web is a minute portion, significantly less than 1%.
Which browser do I need to access the dark web? The most popular option is the Tor Browser. Regular browsers like Chrome or Safari cannot open dark web sites.
Is DuckDuckGo a dark web search engine? No. DuckDuckGo is a privacy-focused surface web engine. It does not index deep or dark web pages.
Can you be tracked on the dark web? Yes—especially through user mistakes. Enabling plugins, downloading files, or logging into personal accounts can expose you. Assume nothing is perfectly anonymous.
Is the dark web more dangerous than the deep web? Absolutely, yes. The deep web is private but legitimate. The dark web is rife with inherently dangerous content: malware, scams, and interactions with criminals.
How do I keep my information off the dark web? You can’t guarantee it, as breaches happen outside your control. However, you can greatly reduce risk: use a password manager, enable 2FA on all sensitive accounts, be vigilant about phishing, and monitor for breaches using services like Have I Been Pwned.
About the Author: Mohammed Khalil is a Cybersecurity Architect specializing in advanced penetration testing and offensive security operations. With certifications including CISSP, OSCP, and OSWE, he has led numerous red team engagements focusing on cloud security, application vulnerabilities, and adversary emulation.